For several years now, antivirus researchers have observed increasing efficiency and sophistication in malware development and distribution. At the start of 2012, I began using the term "industrialization of malware" to describe this phenomenon. I also drew a picture of the fictitious enterprise "Malware, Inc." as a means of conveying the transformation that malware has undergone (the blog has slides about Malware, Inc. that you might find helpful).
As 2012 comes to an end I thought I would discuss in more detail what I think industrialization means in the context of malware, starting with how you industrialize malicious software and why.
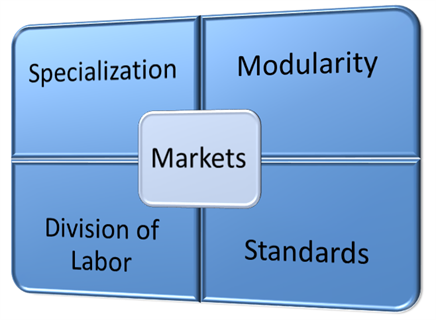
The “how” is the application of well-established industrial or commercial methods. I will consider five of them here: division of labor, specialization, markets, standardization and modularity. The “why” is to maximize profit, which I will illustrate with an ongoing threat, the ransomware attack that tries to frighten people into paying money to the Department of Justice.
 In the early days of criminal malware – defined as code, like viruses Trojans, and worms employed to steal from people and organizations – the malware author and the criminal were often one and the same.
In the early days of criminal malware – defined as code, like viruses Trojans, and worms employed to steal from people and organizations – the malware author and the criminal were often one and the same.
For a person to steal money or data using malware required multiple skills, from coding to network manipulation, from marketing to money laundering (there is a very real sense in which malware has to "sell" in order to be productive and a very real need to turn system compromise into cash to fund operations and generate profits).
In other words, you had to come up with an effective way to trick people, write and distribute the code required, and then reap the financial rewards without getting caught.
Over time, a market-based economy has arisen to supply all of those skills, for a price. This means a criminally minded person can shop around to put together all the pieces of a cyber crime operation without personally possessing all of those different skills. This is a classic case of division of labor, which in turn fosters specialization.
Someone skilled at malware coding can get paid for that skill, and thus improve it, free from the distraction of developing a payment system, and also free from many of the risks inherent in crimeware deployment. The malware coder can sell his skills and output at the going rate in a thriving underground market, but the industrial malware model does not end there.
Driven in part by the law enforcement and internet service provider crackdown on spammers in the last decade, malware authors perfected the technology with which to secretly control large numbers of infected/compromised computers working together as a botnet. In recent years, economic rationalization has driven the evolution from single-purpose botnets, perhaps deployed for either spamming or denial-of-service attacks, to multipurpose botnets, the modular design of which allows different tasks to be pushed to the same collection of compromised machines without having to repeat the infection process.
Here is how ESET malware researcher Jean-Ian Boutin describes Win32/Gataka, an information-stealing Trojan that can read all of your web traffic and alter the balance displayed on your online banking page to hide fraudulent transfers: “It exhibits a modular architecture similar to that of SpyEye, where plugins are required to achieve most of the malware functionality.”
In other words, the infection process can be perfected separately from the exploitation process. and efficiently leveraged through markets. A person might choose to make money from selling or renting infected machines which are then exploited by someone skilled at cashing in on any one of the many possibilities that a botnet presents: distributed denial-of-service (DDoS), data harvesting, spamming, spying, fraudulent bank transactions, and so on.
Consider how ESET senior malware researcher Aleksandr Matrosov describes Win32/Festi, one of the three most active spam botnets worldwide in May of 2012: “Thanks to plugin modules, Win32/Festi is capable of being used for DDoS attacks. The malware's kernel-mode driver implements backdoor functionality and is capable of updating configuration data from the command-and-control server (C&C) and downloading additional dedicated plugins.”
One further evolution now emerging is the standardization of code so that it can be deployed on different botnets. Consider the art of HTML injection or WebInject, which can be used to insert rogue form fields in an otherwise legitimate web page, thereby harvesting additional data from the target. In his most recent post about Win32/Gataka, ESET's Boutin notes,
“In one campaign we have followed, Win32/Gataka botnet operators make use of advanced WebInject configuration that can be used by different types of malware...people specializing in writing WebInject configuration files are able to sell their work to a larger customer-base and are not tied to a particular type of malware. By allowing the script itself to communicate with the control panel, it is easier to implement compatibility with a wide range of information stealing malware.”
We are now seeing the cumulative effects of these industrial factors of standardization: specialization, modularity, division of labor and efficient markets. Better malware can now be deployed faster, and evolved faster to evade detection and improve profitability. Consider the recently discovered Win32/Gapz malware family that uses a new form of code injection and features a novel VBR infection method. Developments like this remind us that moving malware to an industrial model, driven by sound economic principles, has the potential to produce compound benefits, meaning even "better" malware in the future, and more of it.
Recently, network security appliance maker Fortinet devoted much of its 2013 Cyber-Crime Report to describing "The evolution of cyber-crime organizations into well-organized hierarchical operations...organizations [that] rely on a complex network of leaders, engineers, contractors, infantry, affiliates, and money mules to create the attacks that target your network." The report is worth reading for a closer look at the component parts of Crime-as-a-Service (CaaS). I can also recommend this ESET video describing a typical Malware, Inc. operation.




