Protecting your organization against cyber criminals and digital scammers is not easy, and it's certainly not cheap. A vital part of building and maintaining effective defenses is access to security knowledge and expertise, which may not even be a budget item if your organization happens to be an SMB, local government agency, or non-profit. One way to reduce costs in this area is to take advantage of the many free cyber security resources that are available. Sometimes ESET bloggers point to these resources when writing blog posts, but I thought it would be helpful to gather up links to a bunch of resources in one place, everything from malware infection rates to basic information security handbooks. So here we go:
Explore the classics
NIST: To the best of my recollection, the first significant online library of free computer security resources was created by NIST, as in the National Institute of Standards and Technology. Back in 1995, NIST published "An Introduction to Computer Security: The NIST Handbook" also known as SP 800-12.
Since then the 800 series has provided numerous substantial guides on key security topics. A good example is the 24-page "Guidelines for Securing Wireless Local Area Networks (WLANs)" which was published in February of this year. I have always found this series to be a great starting place when you are researching any aspect of cybersecurity. Another good NIST resource is the ITL Bulletin, published by NIST's Information Technology Laboratory, with most bulletins written by the Computer Security Division. These appear monthly.
CERIAS: The Center of Education and Research in Information Assurance and Security at Purdue University has a good Tools & Resources section.
CERT: The Software Engineering Institute at Carnegie Mellon University hosts some very good resources in the areas of Vulnerability Analysis, Cyber Security Engineering, and Insider Threat.
SANS: Known for its security conferences and certifications, SANS also provides a wealth of free cyber security resources such as the InfoSec Reading Room.
Listen to a podcast
For a change of pace, or to keep up with cybersecurity news while you are on the road, or doing the laundry, you might want to tune into the weekly podcasts known as The Malware Report. These can be downloaded as MP3s or tuned in via iTunes. And yes, they do feature ESET bloggers, including Cameron Camp and Aryeh Goretsky. Recent topics include phishing and holiday shopping scams.
Read papers and presentations
When a malware-related topic is too big for a blog post, or has to be presented to a conference, we usually present it as a PDF document. These publications are freely available with no registration required:
White papers: Recent additions include an extensive look at phishing techniques and defensive tactics from David Harley and Urban Schrott, as well as Aryeh Goretsky's widely quoted analysis of Windows 8.
Conference papers: Highlights include analysis of the Festi botnet by Aleksandr Matrosov and Eugene Rodionov which won Best Paper Award at the recent AVAR conference in China (the leading anti-malware conference in the Asia/Pacific region). Another timely paper, delivered at VirusBulletin 2012, is "My PC has 32,539 errors: how telephone support scams really work," by David Harley, Martijn Grooten, Steven Burn and Craig Johnston.
Articles: These include David Harley's piece in Computer Weekly's Security Think Tank: "Are companies too confident about targeted attacks?"
Global threat reports: Every month here at ESET we combine recent output from our worldwide network of security researchers with the latest Live Grid malware detection statistics and publish it as the Global threat report. You can find five years of reports here.
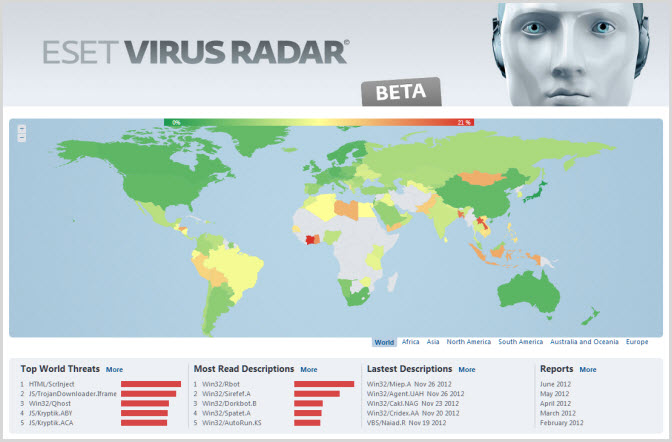
Check the radar
If you are looking for information about malware infection activity and want something more interactive, ESET Virus Radar offers a different kind of resource. The top five malware threats worldwide are listed in near real time and, using a global atlas interface, ESET Virus Radar shows you what is happening around the world. You can then drill down into country-specific malware infection data.
Catch a webinar
Every month or so, one or more ESET security researchers will deliver a webcast (webinar) via a service called Brighttalk. These webcasts often include informal audience polls and question-and-answer sessions. The webcasts are recorded so that you can watch them at any time. We offer a library of more than 50 of security webcasts. (You will need to go through a one-time registration process to access this content.)
Educate all users
With the right information security awareness and training your employees can become a self-policing workforce, greatly improving the effectiveness of your cyber security efforts. The resources at Securing Our eCity are a good place to start. Remember, everyone is a computer user these days and employees will value the information you give them about security risks and the right steps to mitigate them, particularly if you show them how that information can help them protect their personal information.
Any other infosec resources?
I hope you find this post to be a useful introduction to free information security resources. If there are other resources that you think would be helpful in your efforts to defend your data and your systems, please let us know. We will research them and share them here.