A crime wave of malware that demands money from victims to avoid prosecution by the FBI has been alarming web surfers across America. Victims suddenly find their computer frozen, and an official-looking page, like the one shown below, is displayed in their web browser. The FBI and the Internet Crime Complaint Center (IC3) have received so many calls about this scam that they issued a detailed alert last week.
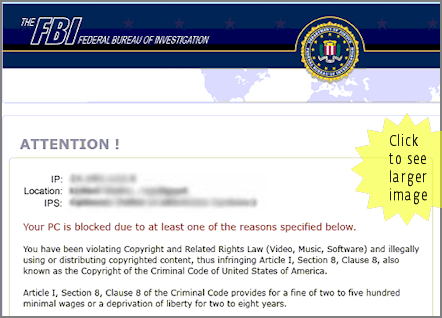 The three most important things to know about this web page are:
The three most important things to know about this web page are:
1. It is not from the FBI;
2. People should NOT follow the instructions on this page;
3. People who see this page have probably been infected with a piece of malware called Reveton.
How did they get infected? That's a good question, one to which I will turn in a moment, but the first order of business is to ensure that as many people as possible are protected against this malware. That means checking that you are running a good antivirus program and that you are keeping it up-to-date. While the scale of this outbreak is making news, Reveton is not a new piece of malware and this is not a new scam, but the bad guys are constantly changing the files used to commit this crime and your antivirus software needs to be updated regularly to catch new versions as they become known. (It is possible for an AV program such as ESET Nod32 to detect and block new variants using heuristics, but you should be running the latest version to ensure maximum protection.)
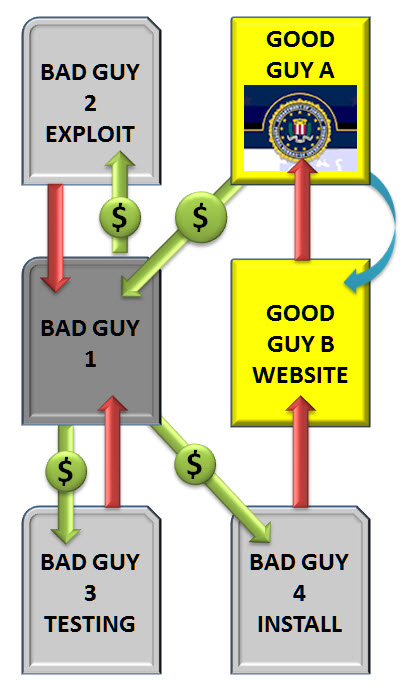 To understand how the scammers operate, we created an overview of the criminal activity involved in this type of scheme. (Bear in mind this is a simplified version of events; often there are more steps and process involved in actually executing this scam.)
To understand how the scammers operate, we created an overview of the criminal activity involved in this type of scheme. (Bear in mind this is a simplified version of events; often there are more steps and process involved in actually executing this scam.)
Here is how Bad Guy 1 rips off Good Guy A.
Bad Guy 1 buys exploit software from Bad Guy 2. Using this software Bad Guy 1 creates a piece of malware that that can take over a victim's computer and demand money.
Bad Guy 1 then pays Bad Guy 3 to test and tweak the malware to increase its chances of evading detection by antivirus programs. A fourth bad guy is then paid to secretly place the malware on an innocent website, in this case the website of Good Guy B.
When Good Guy A innocently clicks on a link to visit the website of Good Guy B the malware installed there is immediately loaded onto Good Guy A's computer and the demand for money is presented.
Bad Guy 1 makes back his investment in this scheme, plus profit, when enough people like Good Guy A send him money to unfreeze their system. How do victims like Good Guy A send the money? This can vary and similar scams in Europe have used systems like Ukash and Paysafe. This example uses MoneyPak, also known as "green dot" which is a service you may have seen in your local Walgreens, Walmart or Rite Aid.
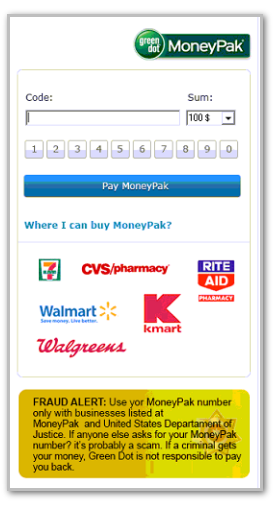 While we don't want to make any assumptions about the demographics targeted by this scam, MoneyPak is marketed as a payment method for folks who don't have a bank account (around 20 million Americans rely on forms of payment other than banks, according to the FDIC).
While we don't want to make any assumptions about the demographics targeted by this scam, MoneyPak is marketed as a payment method for folks who don't have a bank account (around 20 million Americans rely on forms of payment other than banks, according to the FDIC).
As you can see from the payment portion of the scam page, all you need to do to send money to the bad guys is enter the code from the back of a MoneyPak card to which you have added funds.
How much money does such a scheme make for the bad guys? Our good friend Brian Krebs over at Krebs on Security suggests it is plausible that the bad guys are raking in as much as $50,000 per day. Note that these are not bank transferred funds which a bank, or scam victim, can trace and get back. MoneyPak makes that clear in a prominent disclaimer on their website, which the bad guys audaciously exploit by changing the wording to include the Department of Justice, the alleged payee in this fraud.
And how do you get infected? One method we have seen is for the bad guys to install the malware infection process on a perfectly ordinary website, such as a local newspaper or blog. People visit the site in the normal course of their web-surfing and are then infected. This type of attack is called a drive-by and while it can be "enhanced" through a variety of ploys that trick people into visiting infected sites (like SEO-poisoning or spam campaigns) is also preys on entirely innocent and random victims. The number of websites being compromised every day for the delivery of malware like this is now in the thousands. A good web browser will help you avoid these infected sites, as will a good antivirus program.
No doubt the FBI is working hard to catch the people behind this scam, which takes the agency's name in vain as well as generating a lot of calls to agency from concerned consumers. While there is little comfort to be found in the fact that this type of scam has already been hitting European consumers for some time, as noted by my colleague Cameron Camp last year, it is possible that international cooperation among the many law enforcement agencies that have now been "targeted" will speed the apprehension process.




