Andrew Lee just drew my attention to a poll carried out by an IT magazine in the UK, asking the question ‘Do you think it's necessary to use paid-for anti-virus software to effectively protect your PC?’ Clearly this is a question that a lot of people ask, but the answer is more complicated than you might think. [Note: After this post was published, Andrew made a couple of additional comments that I thought were worth including in the main text and you can find them here.] Now on to the survey, and the three answers it offers, in case you feel like responding to it:
- Yes
- No
- Not Sure
 But before you rush off to the web site to tick/check one of those boxes, let me tell you why this is the wrong question. (Unless they'll let you select all three.)
But before you rush off to the web site to tick/check one of those boxes, let me tell you why this is the wrong question. (Unless they'll let you select all three.)
- Firstly, it assumes that anti-virus software can effectively protect your PC. It can, but not all by itself. It only defends against a subset (albeit a large subset) of the threats that are ranged against even home users today. It doesn’t catch all malware. So it doesn’t provide complete, stand-alone protection.
- Secondly, it assumes that free anti-virus is as effective as a scanner you have to pay for. And in some respects, it often is. But just as there is more to protection than anti-virus, so there is more to anti-virus than the number of malicious programs it can detect.
That was the executive summary. Now I’ve got your attention (I hope), let me get to the (slightly) more technical detail.
How do you define protection?
If the answer is along the lines of “if I install AV (free or for-fee), I don’t have to worry about security any more”, I’m afraid you’re wrong. In fact, there are no 100% effective technical solutions that absolve the customer (consumer or enterprise) of the need to take some responsibility for their own protection. The most effective way of countering the full range of threats is to make use of several layers of protection. 
The days when the only threat you needed to worry about was the traditional virus (or, more accurately, malicious software in general) are long, long gone, which is why nearly all major vendors have, somewhere in their product range, integrated their stand-alone AV technology into some form of security suite like ESET Smart Security.
Of course, you don’t have to use a pre-cooked security suite: you can mix and match anti-virus, a firewall, anti-spam and so forth from different sources, if you feel happy to be your own system integrator. And that’s why most vendors still have a stand-alone virus scanner in their product range, as well as multi-functional security suites. The point is that in most circumstances, you need a multi-layered solution, so that you’re not dependent on a single technology to counter the full gamut of threats.
Strictly speaking, a modern AV scanner isn’t a single technology, either: it includes a range of detection techniques from exact identification (the nearest thing to the popular perception of a static ‘signature’), to dynamic analysis (heuristics, active behaviour analysis through emulation or sandboxing), to whitelisting and various cloud-based approaches, to vulnerability scanning. But the primary output of the scanning process is nearly always the detection (hopefully) of known or unknown malware. Other kinds of attack (various forms of phish, exploits that aren’t integrated into malware, and so on) may be better countered by other technologies.
Security Without Anti-Virus
Having said that, apparently real security professionals don’t use anti-virus nowadays (see Security professionals DO use anti-virus). That, at any rate, is the view of sectors of the security industry who don’t, traditionally, sympathise with (or necessarily fully understand) the culture or the technology, and have a vested, commercial interest in other technologies. While I can assure you that there are plenty of security people who do use AV in appropriate contexts, there are circumstances where you might not need it:
- If you have the knowledge (and the resources) to install and maintain more generic security software properly on every system for which you are responsible. Clearly, that doesn’t sound like your everyday user, who generally sees an advantage to software that tells him clearly when it detects a malware problem. There is plenty of effective software that works by blocking anything that could possibly be malicious, or by possible breaches to the attention of an administrator. (And make no mistake: if you have a home computer, you probably are, by default, its administrator, whether you think of yourself in those terms or not.) The fact is, though, that most home users don’t want the potential inconvenience of more generic solutions. I’m not saying that they’re right or wrong: it’s just the way many people are.
- if your system can't trade data or applications with other systems
- If you aren’t required (legally, or by policy or contract) to take every reasonable countermeasure to protect your systems, your data, your staff and your customers. Again, if you’re only responsible for your home system, that doesn’t mean you don’t have an obligation to keep your systems clean by all reasonable means. In some cases, for example, you may find your network services are withdrawn by your ISP, or financial services by your bank or credit card provider, because you don’t have an effective point solution.
- If you’re using an operating system that doesn’t enjoy a significant malware problem. Unfortunately, those seem to be getting fewer… Or if there is no way that your system can trade (possibly boobytrapped) data or applications with other systems, or install any program that hasn’t been screened and guaranteed benevolent by someone else.
- If you’re positive that you’re too clever to fall for any social engineering ploy.
- If you don’t care about the risks from 0-day or 1-day attacks, or indeed any attack that takes advantage of unpatched systems.
AV doesn’t catch everything, but nor does any other security solution (unless – maybe –systems are locked down systems to a degree that damages usability and business processes). It does, however, do a pretty good job of catching a significant proportion of threats. Isn’t multilayered security using even partly-successful tools better than relying on a single panacea du jour?[]
[New Content]
A point rarely mentioned is the prophylactic effect of AV on the huge amounts of stuff that's already out there. There's so much focus on the 0- or 1-day attacks that people lose sight of the fact that there's a real need to continue to protect from malware - and vulnerabilities - that just don't go away. Read any report you like and you see that some threats persist for a long, long time (Conficker, for example). For some reason the 'anti-AV' lobby rarely takes this into account. In fact this is one of the biggest benefits of having a good AV solution in place (and one of the reasons that more generic products are often reliant upon AV as a supplementary tool for analysis in order to maintenance of their own products).
The chances of being hit by newer malware may be relatively low, and that - coupled with the fact that AV may not always catch those proactively - does indeed mean that AV is never going to be 100% effective against the very latest threats. However, once it is effective (i.e. detection is in place) we no longer need to concern ourselves with those threats, not because they no longer exist, but rather that they have been neutralised. And that also means that cybercriminals have to work harder to keep ahead, which cuts into their profit margins.
Free Fall or Free for All?
So let’s get to that underlying assumption that free anti-virus and for-fee anti-virus do the same job equally well. Consumer magazines and testing organizations like Consumer Reports tell us time and time again that there is no need for their readers to pay for effective AV when there are free scanners available. Indeed, I was somewhat amused recently to find myself taking part in a debate where the opposing view was that AV may be essential, but it’s not worth paying for (see Debate: Anti-virus is essential). (Generally, such debates take the form of a clash of opinions fuelled by opposing vested interests, but they do provide an interesting opportunity to boil a viewpoint down to 100 words.)
While some free AVs are, frankly, worth less than they cost, it is true that in general, free and for-fee versions of AV from the same vendor use the same core engine. But they don’t have the same range of functionality and features. In most cases, they’re there as a sort of extended evaluation tool, intended to give you a taste of how well the basic scanner will work on your system. There is some hope, in other words, that you will at some point pay for the commercial version. Why would you do that? Perhaps because you run into a problem where you actually need the support that isn’t available with the free software, or because you’re in a position to recommend a product you’ve had good experiences with in a context where the free version isn’t legal or appropriate (in a work environment, for example).
In fact, many vendors – including ESET – offer a time-limited free trial, but that usually allows the use of a full product for a month or a few months, and may include full support, whereas when a company makes a scanner available for free, it isn’t expecting to supply free support as well. It could be said that it costs nothing to give away a product to people who wouldn’t pay for it anyway, but providing support services is expensive. Unfortunately, it seems that non-provision of support services may open another door to purveyors of fake AV and fake support, who have already proved adept at stealing the legitimate industry’s clothes.
In fact, there are instances where a commercial-grade AV is given away – at least in part – for altruistic reasons rather than in the hope of significant upselling opportunities. It’s good for the community in general when people who wouldn’t pay for a commercial version of AV are running a decent free program rather than having no protection at all, and it gives the companies kudos and good karma, even if it bites into the sales of vendors who don’t use the same model. But maybe it’s not so good for the community in the long term: there’s a hidden cost.
What would happen if consumers stopped buying commercial AV altogether, preferring to rely on free versions? For many companies, the saving on providing support to individuals would actually offset at least some of the dip in sales, and they’d clearly remain focused on selling into the enterprise (and, of course, continuing to diversify into other security sectors). What if more enterprises bought into the idea that they can spend less on AV or even do without it altogether? Well, there are certainly researchers doing great work on malware outside the AV industry, but I have to wonder what would happen if major AV labs ceased to be economically viable. At the very least, I suspect that the wider security community would become rather more aware of the debt that it owes the AV industry in terms of the background analysis that fuels community exercises such as botnet takedowns.
David Harley
Andrew Lee
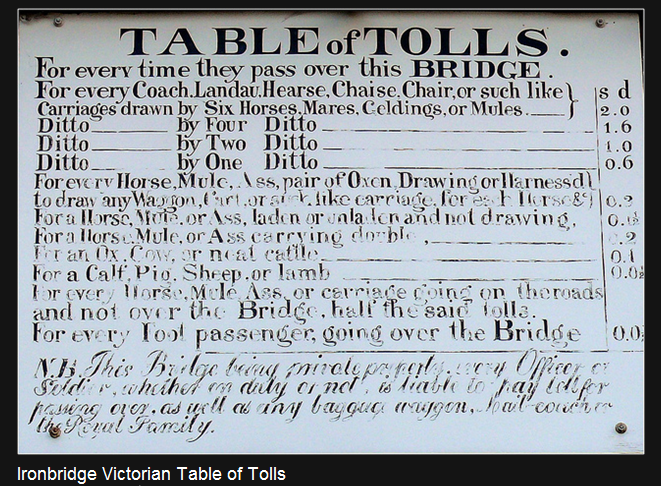
Photographs of toll plaque at Ironbridge, Ludlow castle, and a Tidworth military display by permission of Small Blue-Green World.




