This week we have detected another interesting attack vector. This time cybercriminals are using an interesting technique for hiding malicious Javascripts and employ implicit iFrame injection. At this moment we are tracking hundreds of infected legitimate web sites in the Russian internet segment using this technique of infection. Let’s analyze this attack method step by step. (Since original publication there have been several updates to this story and they are at the bottom of this page.)
If we look at the code on an infected webpage, we can find only one javascript file reference. No malicious iFrame is visible in the source code of infected webpage. In the next stage of our analysis we downloaded this javascript code from one of the infected sites (hxxp://winfield-oil.ru/javascript/script.js) for further analysis.
After analysis we find the interesting javascript function below, using the strange domain name hxxp://onj42a.qpoctushpm.is-an-actor.com/g/: this script is downloaded and executed in the next phase of the attack.
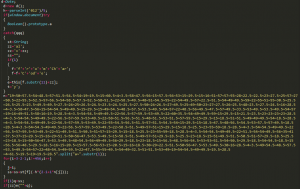
Looking inside this script, we find some really interesting results. Inside the script a big chunk of code is obfuscated with a permutative encoding algorithm.
After deobfuscation the malicious iFrame code looks like this:
A code block inside the iFrame redirects us to the latest version of the Blackhole Nuclear Pack exploit kit.
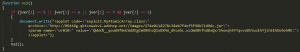
We have tracked some interesting activity through the injected code block with iFrame redirection: Javascript code is used to capture mouse activity with the onmousemove event and only after that does malicious activity continue with the redirection. This activity enabled us to identify a simple method being used to bypass crawlers used by AV companies and others. These are the first steps towards the criminal’s proactive detection of real user activity for tracking detections and bypassing malware collecting by whitehat crawlers.
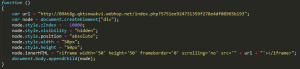
If we look at the Javascript code for exploiting the recent Java vulnerability CVE-2012-0507, we find that a remote Java applet is called using special parameters.
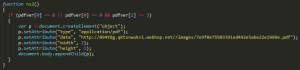
At the next stage of the exploitation process, the malicious java applet at hxxp://094t8g.qktsnwukvi.webhop.net//images/274e0118278c38ab7f4ef5f98b71d9dc.jar (Java/Exploit.CVE-2012-0507.J) uses these parameters for decoding an URL with executable file payload. Without this parameter, the URL can’t be decoded and the attacker can’t follow every step of theattack.
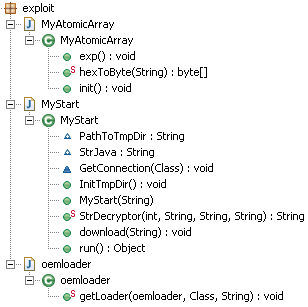
The structure of objects in a Java/Exploit.CVE-2012-0507.J sample looks like this:
The special parameter needed for decoding the URL (hxxp://094t8g.qktsnwukvi.webhop.net/server_privileges.php?7e9f0e75503391ed492e5abe22e1989e=2) serving the payload (in this case it was Win32/TrojanDownloader.Carberp.AH) is found in the method MyStart(String paramString) for the decoding algorithm.
If the Java version on the client side is not vulnerable then the Blackhole Javascript tries instead to attack using the PDF exploit JS/Exploit.Pdfka.PJN (CVE-2010-0188):
Attackers search for ways to extend the lifetime of each obfuscation iteration or each infection of a legitimate website. It’s a natural evolution for drive-by download attacks to include malicious code employing proactive techniques for detectign real user activity and bypassing malware collecting systems.
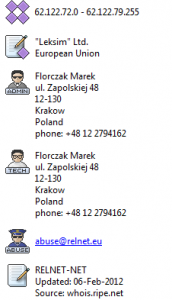
All malicious domains at the time of publication are hosted in the network belonging to Leksim Ltd/RELNET-NET AS5577.
It’s not the first time this hosting provider has been involved in such activities and in April last year we were already seeing incidents originating from this network.
Here’s a list of the more active domains over 24 hours:
- yyzola.gpbbsdhmjm.shacknet.nu
- 64o5uf.inbyepkbja.dvrdns.org
- n6slis.xvseedhxey.homeftp.net
- rjohcj.gpbbsdhmjm.shacknet.nu
- q1y2fi.yuundeswvt.is-a-libertarian.com
- k82f3.neylwuugmd.est-mon-blogueur.com
- gd2wt6.kuppnoynrl.gotdns.org
- bvcydp.kuppnoynrl.gotdns.org
- 41kqki.neylwuugmd.est-mon-blogueur.com
- a0z6o.klsauvnins.dyn-o-saur.com
- lpjbikjwor.kicks-ass.net
- 3u5kj.inbyepkbja.dvrdns.org
- 86xsgn.qktsnwukvi.webhop.net
- 1rgrht.xvseedhxey.homeftp.net
- gmov4d.xvseedhxey.homeftp.net
- dkmcob.xvseedhxey.homeftp.net
- a0z6o.klsauvnins.dyn-o-saur.com
- j5pxed.xvseedhxey.homeftp.net
- cynwoltxdo.dnsdojo.org
- 094t8g.qktsnwukvi.webhop.net
Special thanks to Vladimir Kropotov, independent security researcher from Russia, for some of the information used for this post.
Aleksandr Matrosov
David Harley
Updates:
(1) Aleks reports:
On April 3rd IP’s with Blackhole migrated on the latest version of Nuclear Pack.
Proof logs:
- 02/Apr/2012
GET hxxp://dx6ts.yfwumdwyei.is-a-hunter.com/g/3854063525500425.js 62.122.79.32 - 02/Apr/2012
GET hxxp://yfwumdwyei.is-a-hunter.com/main.php?page=4f086f0830a83d5f 62.122.79.32 [Blackhole] - 03/Apr/2012
GET hxxp://094t8g.qktsnwukvi.webhop.net/g/017432546059324.js 62.122.79.41 - 03/Apr/2012
GET hxxp://qktsnwukvi.webhop.net/main.php?page=4f086f0830a83d5f 62.122.79.41 [Blackhole] - 03/Apr/2012
GET hxxp://pqiyoc.qktsnwukvi.webhop.net/g/697079368134578.js 62.122.79.41 - 03/Apr/2012
GET hxxp://094t8g.qktsnwukvi.webhop.net/server_privileges.php?e843aac68e6c4d6126926e60a1781536=2 62.122.79.41 [Nuclear Pack]
(2) Steve Burn points out that AS5577 is actually Root eSolutions/Root SA: Leksim is one of their customers. A post at http://hphosts.blogspot.co.uk/2009/11/crimeware-friendly-isps-root-esolutions.html refers.
[Further update: there's a useful report of a major Nuclear Pack-related incident from Fox-IT at http://blog.fox-it.com/2012/03/16/post-mortem-report-on-the-sinowallnu-nl-incident/. However, in the case that Aleksandr has been looking at, there's an updated version that includes Java/Exploit.CVE-2012-0507.]
[Update: it turns out that it's not Blackhole, but Nuclear Pack Version 2.0. Our apologies for the confusion. I'm hoping we'll have more information for you shortly.]