My Russian colleagues Aleksandr Matrosov and Eugene Rodionov have found some time to do some more analysis on Win32/Duqu. (Don’t you guys sleep?) In the previous post they concentrated on analyzing the Duqu configuration file format and extracting the exact date on which the system was infected. This time they investigated Duqu’s RPC (Remote Procedure Call) mechanism: since RPC constitutes one of the most interesting features of Stuxnet, they figured that the same might apply to Duqu. Here are their conclusions.
One of the samples of Duqu they analyzed implements an RPC server which is restricted to local use. One of the reasons for implementing such functionality is that it allows malware to avoid detection by security software. We wanted a deeper look at the RPC server implemented by Duqu and to compare it with that used by Stuxnet. In the course of research we found that the RPC routines found in Duqu constitute a subset of the routines found in Stuxnet.
In the figure below we compare the routines responsible for initializing the RPC communication protocol found in one of the modifications of Duqu to the implementation in Stuxnet. These appear to be quite similar to each other and thus reinforce the idea that both threats are likely to be based on the same set of sources. We analyzed Stuxnet’s RPC server in our report (Stuxnet under the Microscope, http://go.eset.com/us/resources/white-papers/Stuxnet_Under_the_Microscope.pdf pp. 56-57).
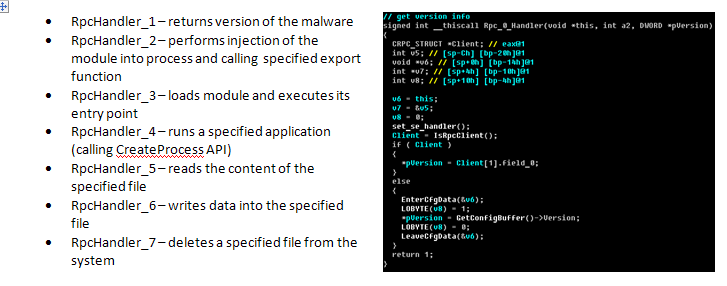
Here is the description of RPC routines implemented in Duqu:
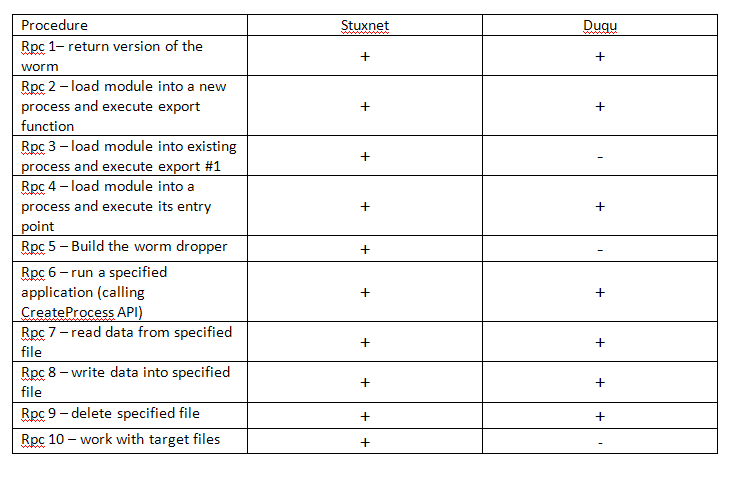
There is a degree of similarity between Duqu’s RPC server implementation and that of Stuxnet. Stuxnet implements 10 RPC procedures while Duqu only 7. At the same time all the RPC procedures implemented in Duqu are present in the Stuxnet code, as is summarized in the next table. RPC routines sorted according to their presentation in the Stuxnet code.