Among the many different trojans that spread on Facebook, something popped up recently that caught our particular attention. The threat, detected by ESET as Win32/Delf.QCZ, is interesting for several reasons.
Distribution
First, let’s look at the distribution vector. Win32/Delf.QCZ relies on the old “fake codec/media player trick” and links to the malware-laden site are spread via Facebook chat – in principle this is hardly innovative. But the malware authors have improved the social engineering factor in this ploy by “personalizing” the attack against the target user. Not only do the spam messages appear to be sent by a Facebook friend, rather than sending a typical generic message (or Facebook wall post) such as “WOW! http://_malicious_link_”, but the malware component responsible for spreading Win32/Delf.QCZ also imitates a conversation before sending the malicious URL. This is shown in the screenshot below, where we have created a Facebook account for demonstration purposes and added “her” as a friend. Obviously, the technique is not perfect: if you interact with the bot, there will be no meaningful conversation. Furthermore, the messages are always in English, irrespective of whether that’s the infected user’s native language.
The link points to a web-page that looks like YouTube, but claims that in order to watch the video you need to upgrade your Adobe Flash Player. To gain the victim’s further trust and spark his curiosity so as to get him to run the malware, the target user’s name (taken from Facebook) is included in the title of the “sensational” video. Furthermore, it’s made to look that the victim’s Facebook friends have commented on it. Here’s an example of some of the comments:
He must have been shamed to do that :)))
I had to update Flash Player, but it was worth it :)) this video is the very best!
one word for it – TERRIBLE!!
Payload
While the distribution vector used by Win32/Delf.QCZ is interesting and effective, its payload is even more intriguing. The trojan could be classified as a fake antivirus, however its attack scenario is different from that of a typical Rogue AV – it doesn’t try to persuade the user to buy a bogus security application. Instead, it tries to imitate the legitimate antivirus installed on the victim’s PC (if any) by displaying a virus alert made to look as if it came from the real AV, which has, in fact, just been removed. Let’s look at how…
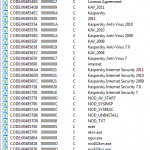
First, the trojan detects what AV solution is installed by going through the list of running processes and looking for process names belonging to security software. The malicious executable contains a list of strings associated with different antiviruses – process names, folder names, etc. (The screenshot below shows only a small fragment of the AV-related list of strings inside the malicious binary.)
Once the trojan has figured out AV it’s standing against, it prepares for an ugly maneuver to remove it. The trick is to remove the AV’s file directory in Safe Mode. Two possible methods are used to get the malware to run after a restart:
- By means of a service: The service created by Win32/Delf.QCZ is named wxpdrivers. The following Registry entries ensure that it’s loaded in Safe Mode:
- [HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlSafeBootMinimalwxpdrivers] "(Default)" = "Service"
- [HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlSafeBootNetworkwxpdrivers] "(Default)" = "Service"
- By making use of the AlternateShell parameter: Overwrites the default executable (cmd.exe) to be run when the Safe mode with Command Prompt option is selected with the malware’s executable (services32.exe):
- [HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlSafeBoot] "AlternateShell" = "services32.exe"
After the malware has registered to run in Safe Mode, it needs to actually boot into it. On Windows XP, this is accomplished by modifying the boot.ini file:
- multi(0)disk(0)rdisk(0)partition(1)WINDOWS="Microsoft Windows XP Professional" noexecute=AlwaysOff /fastdetect /safeboot:minimal(alternateshell)
On Windows Vista (and later), bcdedit.exe is used:
- bcdedit32.exe /set safeboot minimal (alternateshell)
These settings result in the operating system booting into the Safe mode with Command Prompt mode. The wxpdrivers service used with Safe mode and Safe mode with networking are probably backup options in case the user presses the F8 key and selects a different option (the malware is obviously also registered to run when Windows is started in Normal mode).
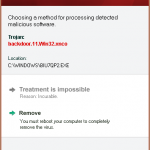
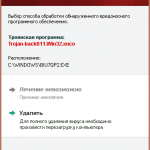
Now all that remains is to restart the system. The trojan silently waits (using Sleep()) for a few minutes in the hope that the user will restart the PC on his own. If this doesn’t happen, a red virus alert is shown claiming that treatment of the detected virus is not possible and that the user needs to reboot. As the screenshots show, a Russian version of the alert is also available and may be used depending on the system locale.
Even if the victim doesn’t click on this option, the malware eventually forces a restart. In Safe Mode, the security solution’s complete file directory is deleted and the system is restarted into Normal Mode.
Aftermath
After all this havoc, the trojan even tries to cover its tracks by fooling the user into believing that the deleted antivirus is still running. The shortcuts to the antivirus are still in place, but now point to a Win32/Delf.QCZ executable.
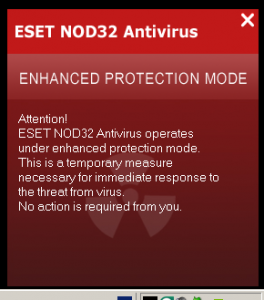
The AV’s system tray icon is also left intact. Well, sort of… When you click on the icon, a window pops up telling you that the product is operating in some kind of temporary “enhanced protection mode”. This window features the security software’s name in the title and description. (A Russian version is also included.)
These are the window titles contained in the malicious executable’s resources:
The trojan also carries the icons used by the impersonated AVs in its resource section:
Motive
After reading about this plot to eliminate the security solution on an infected PC, accompanied by an effective distribution technique, you may wonder what the main purpose of the malware is. The trojan acts as a downloader for other malware. A long list of IP addresses is hard-coded in the executable and another list is also downloaded and saved in %windir%front_ip_list.txt. Such a backdoor is a powerful weapon for further exploitation once the antivirus has been disabled. There is most certainly a financial motive behind this attack scenario. The perpetrators behind Win32/Delf.QCZ could possibly be part of a pay-per-install scheme and rake profits for each successful installation of 3rd party malware.
ESET security solutions detect and eliminate this threat before it is able to launch and the enhanced HIPS (Host Intrusion Prevention System) functionality goes even further by protecting sensitive areas of the Windows operating system.
You can also find a description of this trojan in our Threat Encyclopaedia: Win32/Delf.QCZ.
Robert Lipovsky
Malware Researcher