Our colleagues Aleksandr Matrosov and Eugene Rodionov are tracking the evolution of TDL4 (also known as Win32/Olmarik). The following is a report on the latest TDL4 update, released last week.
In our previous blog post, we described how the latest Microsoft Security Update modified the Windows OS loader (winloader.exe) to fix a vulnerability that allowed the loading of unsigned kernel-mode drivers. This vulnerability was used by TDL4 to bypass the code-signing policy and load its unsigned driver. However, an updated version of the TDL4 bootkit was released last week to work around this patch: modifications in the ldr16 component of TDL4 bring back the ability to successfully infect x64 architecture. In addition to this fix, the low-level kernel-mode hooks of storage miniport driver was improved to provide better protection against detection and removal.
The latest patch from Microsoft has made it impossible to abuse the WinPE mode to bypass kernel-mode code-signing policies. The programmers of TDL4 had to change their tactic to infect 64 bits operating systems. The idea remains the same: modify the ld32 or ldr64 components of kdcom.dll, depending on the system being infected. Instead of switching into WinPE mode, the new version of TDL4 patches the I_CheckImageHashInCatalog routine. This routine is used to validate the integrity of the modules being loaded by winload.exe.
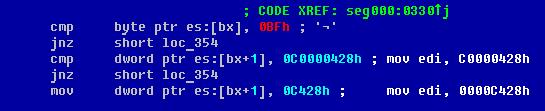
In normal circumstances, when the I_CheckImageHashInCatalog routine fails to verify the integrity of a module, the value 0xC0000428 (STATUS_INVALID_IMAGE_HASH) is returned, preventing the system from booting The TDL4 bootkit patches this routine to make it return 0x0000C428 instead of 0xC0000428. This latest value is not an error code per say (the error codes in kernel-mode usually have the most significant bit set to 1). Hence, the replacement of kdcom.dll is not detected by the operating system. The next figure shows the code responsible for on-the-fly patching of ldr16 in winload.exe:
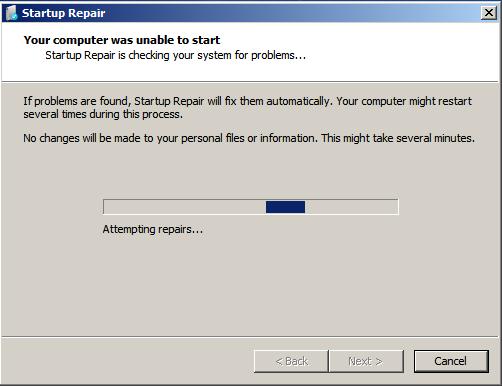
However, it appears this new feature is not completely stable. On some systems, the operating system is able to detect the modifications and launches the Startup Repair, as shown in the following screenshot. After the obligatory reboot, the system becomes totally unbootable.
The second improvement in this new version of TDL4 is in the low-level kernel-mode hooks of storage miniport driver object. The previous versions of the malware hijacked the driver object at the lowest device object in storage device stack as depicted on the figure below:
In this case, we can easily gain access to the miniport device object (Hard drive PDO) and then walk through the list of its adjacent device objects to get a pointer to the “real” hard drive miniport driver object. The new version of TDL4 hides the hard drive miniport driver object in a more sophisticated way:
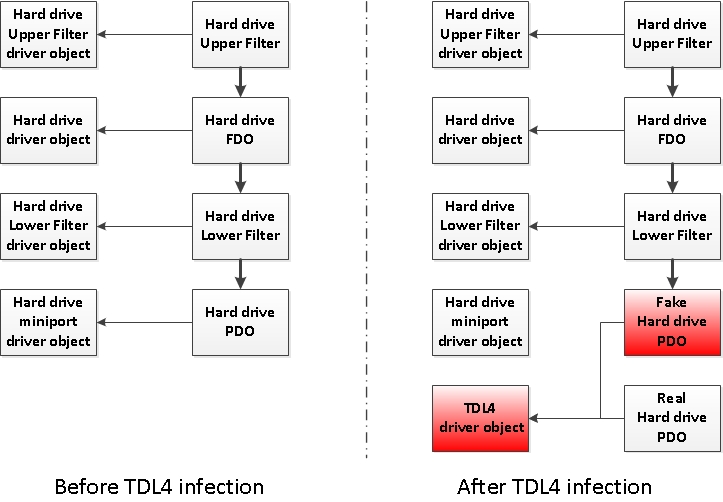
In this case, the lowest device object in the storage device stack is no longer the PDO corresponding to the hard drive. This new modification makes the detection and removal of this malware a much more challenging task. ESET Antivirus detects the latest TDL4 dropper as Win32/Olmarik.AMN and is able to clean infected hosts.
Special thanks to Alexis Dorais-Joncas for his help in preparing this post.




